Around this time last year git added a "smart" HTTP transport that is faster than the old HTTP transport (and in some cases faster than SSH too). And a few months later GitHub added support for this new HTTP transport and made it the default selected url for repositories (that you aren't a contributor for).
There aren't any major advantages using https over ssh to access your GitHub repositories, it's just more simple to use your username/password instead of adding your ssh key. The only other advantages is that it's easier to set up HTTP proxy for git (git config --global http.proxy proxy:8080 vs ssh config) and being able to use more than one GitHub account (which you shouldn't since anyone can add you as a contributor to a project).
One major disadvantage is that it asks you for your username/password each time you interact with your remote repository (clone, pull, push, etc). To solve this, I decided to write a program that stores your username and/or password in your keychain so git will ask once for you username/password and retrieve it later so you don't have to type it again. If you only want the program, skip to it.
Learning
I started writing this program using ruby and some system calls to the security command line tool. But to store a password in your keychain using this tool you have to pass it as an argument to security which means anyone on the system can see this if they know were to look. This quickly ruled out using the security tool so I had to look at using the keychain api natively.
My next step was to search for a gem that wrapped the C api for me so I don't have to get my hand dirty in C. I found the mac-keychain gem and later heard about zenspider's gem osx_keychain. Using native C functions to add the password prevents it from being available in plaintext to other processes which fixes that problem. But I quickly found another problem.
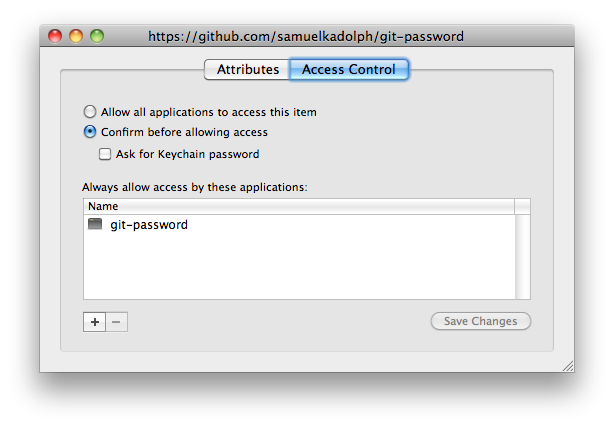
Each OS X Keychain item has a list of authorized applications that can read the password from the item without the user being prompted.
When you add an item to the keychain unless you otherwise specify, the current application running is implicitly the only authorized application. This makes sense because you store passwords to be able to recover their plaintext later (otherwise you should be using key derivation function like bcrypt or scrypt).
The problem is that when you call the native C functions from inside ruby, ruby is the application that is running (your code is just a script that Keychain is unaware of). So this means that any ruby script can freely retrieve the passwords stored by other ruby scripts (and thus enable a rarely large security flaw with your program) without the user being prompted to give permission.
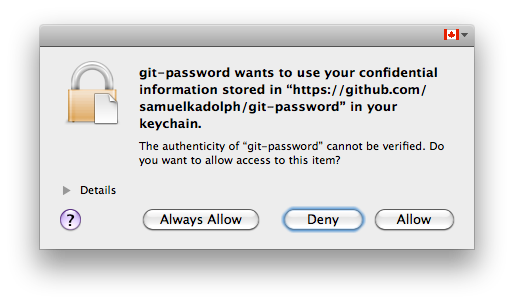
So I had to scrap the idea of using ruby and write my own C program to do it. This would prevent anyone from running code on the computer and being able to freely retrieve passwords stored by my application (along with the application names, a signature is stored so if someone wrote their own application with the same name, it would still prompt the user for access).
The next step was to confirm that git was the one that was calling the program so someone cannot do git-password "Password: " inside of a git repository and have the program give the password up. I took a while but I finally found some sample code that shows how to get the list of processes on OS X and that combined with getppid allows me to check that git was the program that started us (technically it's git-remote-https).
Program
The final fruit of my endeavour is a program called git-password available here. It was written in Xcode 4 and the source is available here.
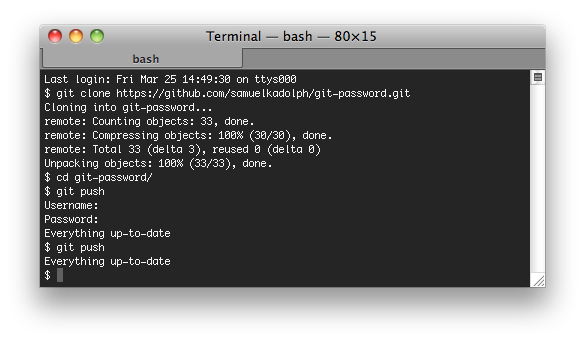
To use the program first you need to download it and make it executable.
curl -L http://bit.ly/git-password > ~/git-password
chmod +x ~/git-passwordAnd now depending on your version of git you have 2 different ways of making git use the program.
Git 1.7.3 and above
git config --global core.askpass ~/git-passwordGit 1.7.2 and below
echo export GIT_ASKPASS="$HOME/git-password" >> .bash_profileAnd now just go and clone any https repository or update the url of your remotes.
/Users/benjaminmoss/git-password: line 1: syntax error near unexpected token
<'You are being redirected.’/Users/benjaminmoss/git-password: line 1:
Github add a redirect on the original url I had. I’ve updated the referenced url and add the -L flag to curl. Thanks for pointing it out.
Thank you for making this awesome tool.
Awesome tool indeed. But another major disadvantage is that this tool prompts and then stores a copy of my GitHub password for each individual repo. This would be great if I was using multiple GitHub accounts, but I don’t (and there’s no reason to) so this “feature” is basically pointless.
Sam: any plans of teaching this tool to keep just one copy of GitHub credentials for all “github.com” repos?
My fork mentioned in another comment at https://github.com/timotm/git-password now has this feature, too – today I ran into the use case of having to clone more than repository from a single server.
Beautiful, the constant password prompts were really annoying me, thank you so much for sharing. I have just started with Git and love it – even more so now!
Hey I couldn’t get this to work, undid all the steps and gave up yet it still keeps asking for username & password… any ideas?
The program is very useful but unfortunetly it doesn’t work with the latest versions of git, Could you fix the problem?
Thanks
I also had some problems in getting it to work with my git version, so I forked and modified a bit. Please see https://github.com/timotm/git-password for details.
There will be a new contrib app in 1.7.9:
https://github.com/gitster/git/blob/master/Documentation/RelNotes/1.7.9.txt#L18
https://github.com/gitster/git/tree/master/contrib/credential/osxkeychain
Beautiful. Such a time saver.
A simpler solution is: http://stackoverflow.com/a/7773374/50878
.netrc with the following:
machine github.com
login
password
That means keeping your github password in plaintext on your computer.
I did this successfully on my other machine, but I just tried on this one and I am now getting the following error whenever trying to push or pull:
fatal: can only be used by git
Could you help please? Thanks!
How do I remove this? I can’t figure out how to unset core.askpass
Never mind, I figured it out. Sorry for the comment spam.
How did you get around this? I’m having the same issue… It worked for me on one computer, but on another I get the same fatal error
Remove the line from ~/.gitconfig that starts with “askpass”.
I happily used git-password (thanks!!), and was wondering if it also works with the credential helpers, introduced in git 1.7.9. (See http://git-scm.com/docs/gitcredentials.html). There is also a osxkeychain helper (see https://github.com/git/git/tree/master/contrib/credential/osxkeychain). For now, I am still using git-password (not al my clients are 1.7.9 yet), but I’m interested in your opinion on this.
Hi, I don’t entirely buy the argument why this is more secure than just using C bindings from Ruby. See https://gist.github.com/4116645 for my argument.
Thanks for making this, it seems to work OK.
However, I’ve noticed that git still keeps a copy of my password in plaintext in ~/.subversion/auth/svn.simple/9d82869915xxxxxxxxx, so it is currently not as helpful as it could be. Is there any way to make it use (only) the Mac keychain?
I have struggled for a few months now with this issue and your solution was the only one that fixed it. THANKS SO MUCH 😀
сытина на божественное исцеление омоложение сердца http://charteronebusinessaccess.xyz/index.php?viewpage=16715 герпес на губе у мужчин вирус папилломы человека
g6687hjhk7
As mentioned before, recent version of git have introduced git-credentials and helpers for many OS.
Read how to use it in the docs here: https://git-scm.com/docs/gitcredentials and avoid breakage.
For me, on MacOS setup was as simple as running: